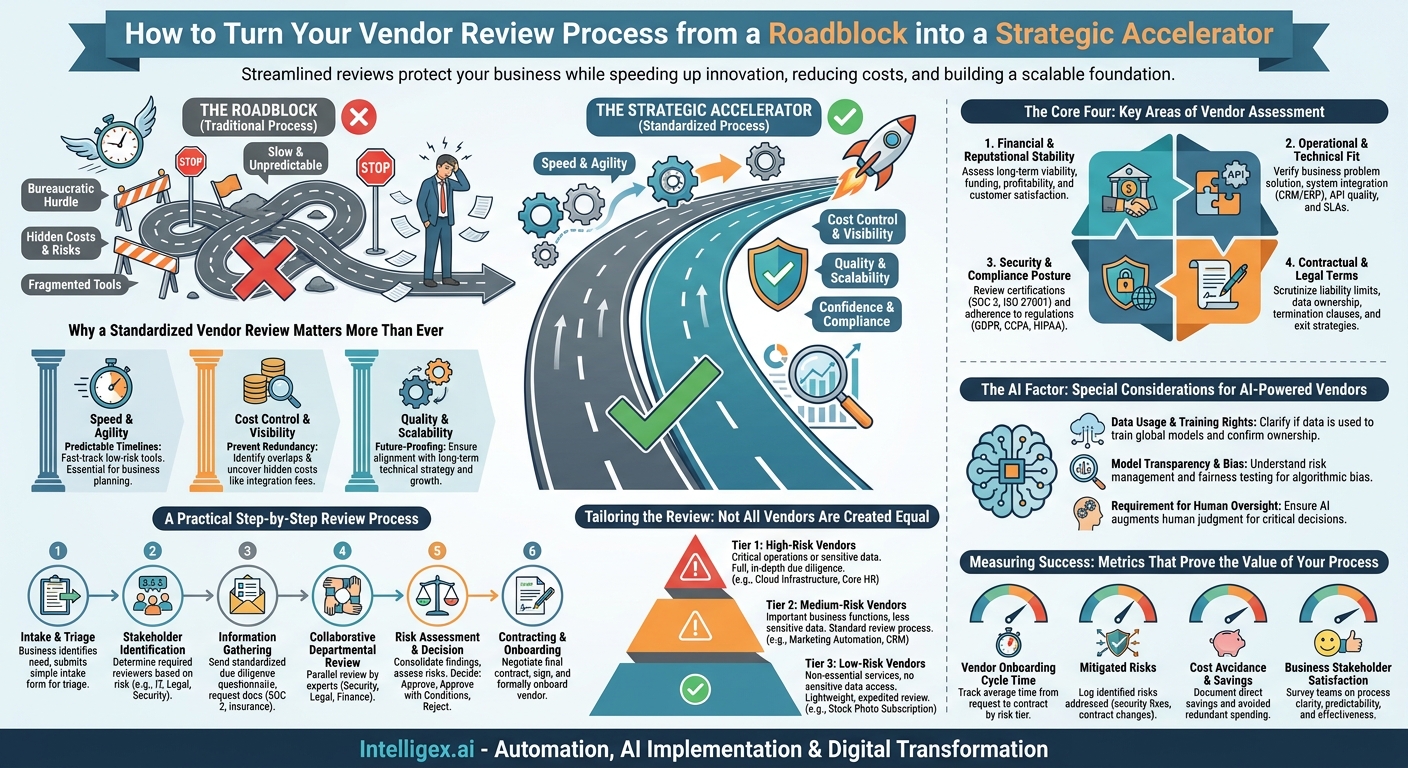
Bringing a new vendor or software tool into your company can feel like a race. Your team has a critical business need, they’ve found a solution, and they want to start using it yesterday. The traditional vendor review process, often seen as a bureaucratic hurdle thrown up by IT, legal, or finance, can feel like a major speed bump. But what if we reframed it? A well-structured vendor risk review isn’t a roadblock. It’s a strategic accelerator that protects your business while helping you move faster, reduce costs, and build a more scalable technology foundation.
When done right, a streamlined review process provides clarity and predictability. Instead of deals getting stuck in an endless loop of emails and security questionnaires, teams know exactly what’s needed to get a new tool approved. This isn’t about saying “no” more often. It’s about getting to a confident “yes” faster and safer. It’s about ensuring the marketing team’s new analytics platform doesn’t create a data privacy liability, or that the finance department’s new automation tool can actually integrate with your existing systems without a massive, hidden IT cost.
Why a Standardized Vendor Review Matters More Than Ever
In today’s fast-paced environment, business units are empowered to find and procure their own software solutions. This autonomy is great for innovation, but without a guiding framework, it can lead to chaos. Disparate tools that don’t talk to each other, redundant spending on similar applications, and serious security vulnerabilities are common side effects. A standardized vendor review process brings order to this chaos, delivering tangible business value across several key areas.
Speed and Agility
A clear, documented process with defined roles and timelines removes ambiguity. When a sales team needs a new enablement tool to hit its quarterly target, they can’t afford to wait six weeks for a security review. A standardized process, especially one that tiers vendors by risk, can fast-track low-risk tools in days, not weeks. It makes the procurement timeline predictable, which is essential for business planning and execution.
Cost Control and Visibility
A central review process prevents redundant spending. It’s common for multiple departments to independently purchase licenses for similar tools, like project management or design software. A vendor review provides a checkpoint to identify these overlaps. Furthermore, it uncovers hidden costs. A vendor’s solution might have a low sticker price, but the review process can reveal expensive integration fees, a lack of essential support in the basic package, or contractual terms that allow for steep price hikes upon renewal.
Quality and Scalability
Does the vendor’s solution actually fit into your long-term technical strategy? A proper review ensures that a new tool aligns with your existing technology stack, meets your standards for performance and reliability, and can scale as your business grows. It prevents the adoption of “shiny object” tools that solve a short-term problem but create a long-term integration and maintenance nightmare for your IT and operations teams.
The Core Four: Key Areas of Vendor Assessment
A comprehensive vendor review doesn’t need to be overwhelmingly complex. Most of the critical risks and considerations fall into four primary domains. By systematically evaluating each vendor against these pillars, you can build a holistic picture of their suitability as a partner. Think of this as your foundational checklist for any new relationship.
1. Financial and Reputational Stability
You are not just buying a product; you are entering a partnership. You need to be confident that your vendor will be around to support you for the duration of your contract. A vendor that is financially unstable could suddenly go out of business, be acquired by a competitor, or drastically cut back on support and product development, leaving you stranded. Key questions include their funding status, profitability, and the size and satisfaction of their customer base.
2. Operational and Technical Fit
This is where the rubber meets the road. Does the solution solve the intended business problem effectively? It’s crucial to look beyond the sales pitch and evaluate the technical reality. How will it integrate with your core systems like your CRM or ERP? Does the vendor provide a well-documented API? What are their support hours and guaranteed response times (Service Level Agreements, or SLAs)? A poor technical fit can turn a promising solution into a costly, time-consuming project for your internal teams.
3. Security and Compliance Posture
In an age of constant cyber threats and stringent data privacy regulations, this is a non-negotiable pillar. You are entrusting the vendor with your company’s data, and potentially your customers’ data. A breach originating from one of your vendors is still your responsibility. You must verify their security practices and their compliance with relevant regulations. This is where you look for certifications and attestations.
- SOC 2 Reports: An audit that validates a vendor’s controls for security, availability, processing integrity, confidentiality, and privacy.
- ISO 27001 Certification: An international standard for managing information security.
- Regulatory Compliance: Adherence to rules like GDPR for European data, CCPA for California consumer data, or HIPAA for health information.
4. Contractual and Legal Terms
The contract is the ultimate source of truth for the relationship. Legal and procurement teams must scrutinize the fine print. Key areas to review include limitations on liability, data ownership clauses (who owns the data you put into their system?), terms for contract termination, and the process for getting your data back if you decide to leave. Unfavorable terms can lock you into a bad relationship or expose you to significant financial risk.
A Practical Step-by-Step Review Process
Having a defined, repeatable process is the key to making vendor reviews efficient and effective. It ensures all necessary steps are taken, all key stakeholders are involved, and the outcomes are documented. The following six-step process can be adapted to fit organizations of any size.
- Intake and Triage: The process begins when a business team identifies a need. They should complete a simple intake form that captures the business case, the type of data the vendor will handle (e.g., public information, internal business data, customer PII), and the estimated cost. This initial information allows you to triage the request and determine the required level of scrutiny.
- Stakeholder Identification: Based on the triage, identify the required reviewers. A low-risk tool might only need review from the business owner and IT. A high-risk platform that will store sensitive customer data will require input from Legal, Information Security, Finance, and the Data Privacy Officer.
- Information Gathering from the Vendor: Send the vendor a standardized due diligence questionnaire. This is far more efficient than an endless chain of ad-hoc emails. Request key documentation upfront, such as their latest SOC 2 Type II report, evidence of insurance, their standard contract, and their public privacy policy.
- Collaborative Departmental Review: Each stakeholder reviews the vendor’s submission from their area of expertise. Information Security assesses the security controls. Legal redlines the contract. Finance analyzes the pricing model and total cost of ownership. This parallel processing is much faster than a sequential review.
- Risk Assessment and Decision: The stakeholders convene to discuss their findings. All identified risks are documented, and their potential impact is assessed. Based on this holistic view, a decision is made: Approve, Approve with Conditions (e.g., specific contractual changes must be made), or Reject. This decision and its justification should be clearly recorded.
- Contracting and Onboarding: Once approved, the final contract is negotiated and signed. The vendor is then formally onboarded according to your company’s procedures, ensuring they have the right access and that your team is properly trained on the new solution.
Tailoring the Review: Not All Vendors Are Created Equal
Applying the same level of intense scrutiny to every vendor is a waste of time and resources. It frustrates business teams and creates bottlenecks. The key to an agile process is to tailor the depth of the review to the level of risk the vendor presents. A risk-based tiering system is the most effective way to achieve this.
Tier 1: High-Risk Vendors
These are vendors that are critical to your operations or that will handle your most sensitive data. They require a full, in-depth review across all four pillars.
Examples: A new cloud infrastructure provider like Amazon Web Services, a core HR and payroll system, or a payment processor that handles customer credit card information.
Review Level: Full due diligence, including deep dives into their security reports, rigorous contract negotiations, and potentially a custom security assessment.
Tier 2: Medium-Risk Vendors
These vendors provide important business functions but are not operationally critical and may handle less sensitive data.
Examples: A marketing automation platform that holds customer email addresses, a project management tool used for internal projects, or a customer relationship management (CRM) system like Salesforce.
Review Level: A standard review process using your questionnaire and a thorough check of their security certifications and contract terms.
Tier 3: Low-Risk Vendors
These are vendors that provide non-essential services and have no access to sensitive company or customer data.
Examples: A subscription for stock photography, a graphic design tool used for marketing materials, or an online training provider.
Review Level: A lightweight, expedited review. Often, these can be handled through a simple checklist or even be pre-approved if they meet certain criteria, requiring only a manager’s sign-off and a check by finance.
The AI Factor: Special Considerations for AI-Powered Vendors
The proliferation of AI-powered tools adds a new layer of complexity to vendor reviews. While the core four pillars still apply, you need to ask more specific questions about how these vendors use your data and how their models operate. Ignoring these factors can introduce significant privacy, ethical, and operational risks.
Data Usage and Training Rights
This is the most critical question: What happens to the data you input into their AI model? The default assumption should never be that it remains private. You must get explicit, contractual confirmation. Is your data used to train their global models for the benefit of all their customers? If so, that may be unacceptable for confidential information. Clarify data ownership, residency, and your right to delete your data from their systems and their models.
Model Transparency and Bias
AI models can sometimes be “black boxes,” making it difficult to understand how they arrive at a decision. For tools used in critical functions like hiring or credit assessment, this is a major risk. Ask the vendor what steps they take to test for and mitigate algorithmic bias. While they may not reveal their proprietary algorithms, they should be able to explain their risk management and fairness testing processes.
Requirement for Human Oversight
Even the most advanced AI is not infallible. A responsible implementation plan often includes a “human-in-the-loop” for critical decisions. An AI tool that screens résumés should flag top candidates for a human recruiter to review, not automatically reject others. Your review should assess whether the tool is designed to augment human judgment or to replace it in a high-stakes context.
Measuring Success: Metrics That Prove the Value of Your Process
To demonstrate the value of a structured vendor review process, you need to track its impact. The right metrics can shift the conversation from “this is a bottleneck” to “this is a business enabler.”
- Vendor Onboarding Cycle Time: Measure the average time from initial request to a signed contract. Track this metric separately for each risk tier. Your goal should be to significantly shorten the time for low-risk vendors while maintaining diligence for high-risk ones.
- Mitigated Risks: Keep a log of the risks identified and addressed during the review process. This could include security vulnerabilities that were fixed, unfavorable contract terms that were renegotiated, or compliance gaps that were closed before signing.
- Cost Avoidance and Savings: Track direct cost savings from negotiating better pricing or payment terms. Also, document cost avoidance by preventing the purchase of redundant software or tools that would have required expensive, unplanned integration work.
- Business Stakeholder Satisfaction: Periodically survey the business teams who use the process. Is it clear? Is it predictable? Do they feel it helps them select better tools? Their feedback is essential for continuous improvement.
Getting Started: Your Immediate Next Steps
Implementing a formal vendor risk process can seem daunting, but you can start small and build momentum. You don’t need a complex system from day one. Focus on creating a foundation of clarity and consistency.
1. Map Your Current State: Before you build anything new, understand what happens today. When a team wants a new tool, who do they ask? What documents do they provide? Where do requests get stuck? Simply visualizing the current ad-hoc process will reveal the biggest pain points to solve first.
2. Create a Single Front Door: Establish one simple intake form or email alias for all new vendor requests. This is the most important first step. It gives you visibility into the pipeline of new tools and provides a single point of control for initiating the review.
3. Define Simple Risk Tiers: Start with basic definitions for low, medium, and high risk based on data sensitivity and business criticality. This allows you to immediately begin fast-tracking the easy, low-risk requests, which will build goodwill and show value to your business partners.
4. Communicate the “Why”: As you roll out the process, focus on education. Explain to your teams how this framework helps them achieve their goals faster and more safely. Frame it as a service designed to support them in making smart, secure, and cost-effective technology decisions. When they understand the value, they will become your biggest advocates.
Category:
Get a FREE
Proof of Concept
& Consultation
No Cost, No Commitment!